They aim to ensure that only shoppers who’re sure about their freelancing work can provide services on their platform. There are a number of platforms to start your Python freelance experiences. Attending local networking events is one other glorious approach to meet potential clients face-to-face. These occasions let you showcase your abilities and make priceless connections in individual.
Rates may vary from ₹500 to ₹2500 or more, relying on the precise abilities required and the scope of the Python growth work. I am a passionate coder with abilities and experience in Python and knowledge science and also have deep understanding and implementation information of Airtificial intel… Learn how it can safeguard your business’s funds and enhance progress.
Data visualization makes it easier for viewers to understand complex info at a glance. By presenting information visually appealingly, such as graphs or charts, viewers can quickly grasp crucial insights and tendencies without studying via prolonged stories or code snippets. LinkedIn can be an excellent useful resource for researching firms hiring Python builders.
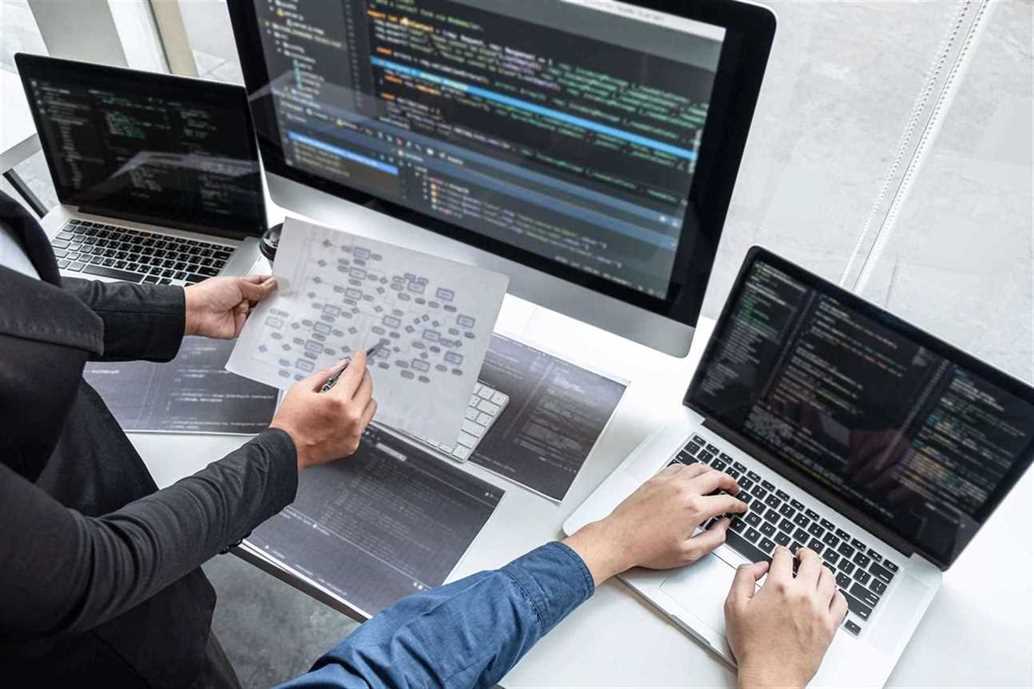
A great library ecosystem is an often-cited advantage of the Python language. That means that profitable Python software program engineers can use many mixtures of Python tools and languages to accomplish project goals. These Python developers are often skilled in, and comfy with, a suite of well-liked Python programming and scripting languages, frameworks, and tools. Collaboration with other developers is an excellent method to learn new strategies and best practices in programming languages like Python. As a freelancer, it is important to network with different developers who share related interests or work on associated tasks. Determining your hourly fee is crucial as a contract Python developer to guarantee you earn what you deserve.
Tips On How To Turn Out To Be A Python Developer
For instance, you can develop software program purposes that help people with disabilities. You can do some initiatives for free to build your portfolio or construct web sites for charities. These tasks not solely present revenue but in addition contribute positively to society.
- Alex is a developer with 6+ years of experience in Python, JavaScript, SQL, and R.
- Understand the position and impact of an SAP CRM Developer on enterprise operations.
- In many situations, yield is used within a loop, mechanically producing a massive number of elements.
- Generators are commonly used to explain an infinite collection.
If you utilize AI you will find it is not going to appropriately translate the code. You will need to test your code in opposition to multiple receipts to capture the variations they have (price every, price per OZ, &quo…
Are Ai Builders In Demand? Discover The Rising Need For Ai Talent In Enterprise
If it is a straightforward task that requires minimal effort, charging lower than the market fee may be acceptable. However, setting higher-than-average rates is reasonable if the project includes advanced coding or distinctive skills. Once you’ve created a powerful portfolio, the next step is to make it simply accessible to potential purchasers.
It’s essential to have a robust one that showcases your abilities, experience, and tasks to potential shoppers. The best way to do this is by building real-world applications demonstrating your language proficiency. Web growth, information science, and machine learning are some areas where Python language is widely used. Web developers use frameworks similar to Django or Flask to create web sites using Python. Data scientists use libraries like NumPy and Pandas for data analysis and visualization. Hiring a Python Developer in Bangalore offers access to a talent pool in certainly one of India’s main tech hubs.
Ideal for non-tech business leaders looking for clear, straightforward insights. Discover how Teamcubate’s expertise in cybersecurity risk administration can safeguard your business. Protect your digital belongings with our comprehensive, easy-to-understand strategies. Discover the necessities of risk administration in an easy, easy-to-understand information. Perfect for enterprise homeowners in search of sensible methods for minimizing dangers and maximizing success. Teamcubate’s guide helps businesses like yours to attach with top tech talent, streamlining your recruitment course of.
Discover Your Best Threat Manager: A Simple Information To Crafting The Proper Job Description
The first step is to determine your rate based mostly in your expertise and experience. If you are just beginning, it’s essential to analysis the market charges for freelancers with related expertise and expertise in your area. To turn into a profitable freelancer Python programmer, you need extra than just programming expertise. You must know the frameworks and libraries required for varied tasks. This will allow you to choose the proper tools for every project, making certain environment friendly growth processes whereas freelancing.

Understand the monetary benefits and strategic features from AI expertise. Discover the highest 10 SaaS instruments each startup wants in 2024. Boost your productivity, handle projects, and develop your small business with these important instruments. Freelancing as a Python developer requires devotion and patience. If you are a beginner, you have to take time to learn and get some experience. According to ZipRecruiter, Python freelance salaries vary between $85,000 to $138,500 within the United States.
Clearly outline your project requirements, evaluate portfolios, and consider freelancers with a robust background in Python improvement. Conduct interviews to assess their expertise and understanding of your project. To find a contract Python Programmer near Mumbai, go to the official Truelancer web site. Freelancers can tackle particular projects or contribute to ongoing growth, providing scalable options tailor-made to your distinctive wants.
What Is A Full Stack Sap Developer? – Important Information For Enterprise Leaders
Using Truelancer.com is one hundred pc secure as the cash is launched to the freelancers after you’re 100 percent happy with the work. Discover key methods to hire skilled SAP developers effectively. Learn tips on how to streamline your hiring course of and ensure you choose the best talent for your business wants. One of the challenges freelancers face is setting rates hire freelance python developer that precisely replicate the worth of their work. It’s essential to track your hours and set rates based on the project’s complexity, your experience stage, and the required time. Igor is a results-driven quantitative development skilled with progressive industry experience in commodities, deep learning, computer imaginative and prescient, and data science.
Send your clients on your website from your freelance profile. Your skilled web site will distinguish you from the opponents. Each platform has its personal coverage and, thus, taxes they may charge. So, before you make a profile on your chosen platform, get to know their work coverage. This signifies that you can not anticipate a high wage to begin with. As they turn into more popular, they become a freelancing market.
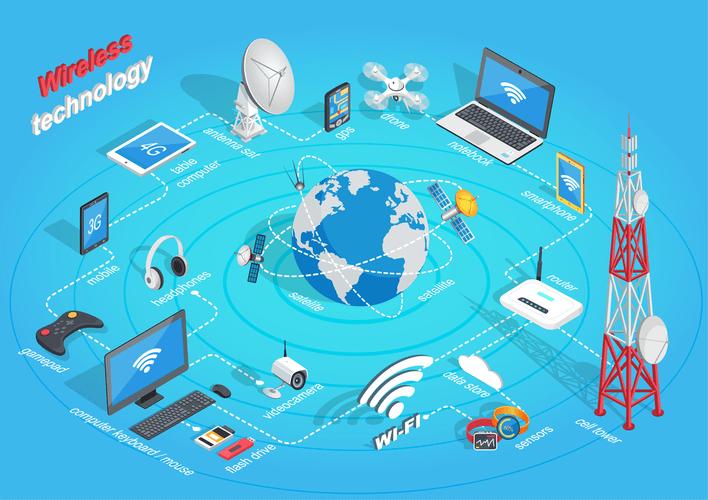
Freelancers can work on particular initiatives, provide tailor-made options, and adapt to your project necessities. Python is widely used for web development, information science, artificial intelligence, and more. Businesses and organizations hire Python builders to leverage the language’s versatility and intensive libraries for diverse initiatives.

Professional builders with high incomes rates are making €163,500 annually. Developer’s location, expertise, and the complexity of the project. According to Glassdoor, the common annual wage of a Python freelance developer is between €99,000 and €164,000.
The Best Practices For Hiring A React Developer – Simplify Your Hiring Process
As for full-time distant Python developers for hire, you’ll be able to expect to make a successful hire in 14 days. To lengthen a contract engagement to a full-time hire, a contract-to-hire charge will apply. The world demand for Python builders is skyrocketing, so put together for a serious search for new and experienced programming expertise. Here are a few suggestions designed for hiring managers engaged within the hunt.
Provide your portfolio and ensure you are available on your purchasers. It is a superb option for building your portfolio before making use of for a job in a company. This is as a end result of these platforms get thousands of purposes every day. To ensure a selected degree of service quality, they have to be selective.

Understand their abilities, duties, and the way they contribute to enterprise growth. Discover why AI builders are crucial for companies right now. Learn in regards to the rising demand for AI skills and how it impacts your corporation growth and innovation. You solely need to promote your services in case you are sure of your abilities. But gaining expertise and studying extra will make you extra confident. Your companies will benefit clients who lack programming abilities or have limited time.
Sap App Growth: Streamlining Business Processes
Read more about https://www.globalcloudteam.com/ here. Our development team will help you develop your projects. We specialize in the implementation of artificial intelligence and machine learning of various levels of complexity.